10 April 2026
The Ultimate Master Guide: AI-Powered Video Production for Professionals (2026)
How to Build a High-Efficiency Workflow with Next-Gen Hardware and Generative AI In 2026, the boundary between “technical expertise” and…
10 April 2026
How to Fix “Audio Renderer Error. Please Restart Your Computer” on YouTube (2026 Guide)
If you’ve encountered the dreaded “Audio Renderer Error. Please restart your computer” message while trying to watch a YouTube video,…
8 April 2026
What Is Zero Trust Security? Architecture, Principles, and Real-World Use Cases
Cybersecurity used to rely heavily on a simple assumption: once a user or device was inside the network, it could…
8 April 2026
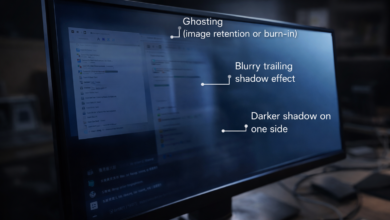
Shadow on Computer Monitor: Causes, Fixes, and When It Means Hardware Failure
A shadow on a computer monitor can show up in several ways: a faint duplicate image, a dark patch on…